It’s not difficult to create a strong password

Everyone uses passwords. They suck. I don’t know anybody who signs up for a new account and says: “yay, I get to create a new password”. Unfortunately, at the moment, they are a necessary evil.
Even if you don’t read the rest of this blog, please follow this one piece of advice: use a password manager with a single, strong master password. I’ll talk about password managers in more detail later in this blog.
The hard truth
There is no such thing as an uncrackable password. If someone had no time constrains and was able to try every combination of numbers, letters and characters, they would eventually crack your password. What we need to do is make it as difficult as possible for them to guess it.
In most situations, it’s not actually one person sitting at their computer trying to guess a password, typing it into the password box and seeing if it works. It is a computer, or a cluster of computers, trying hundreds or, in some situations, thousands of passwords every second.
If your password has fewer than 8 characters, it can probably be cracked within a day on an average desktop computer, even if it contains symbols. As computers get more and more powerful, it becomes easier and easier for computers to guess passwords.
In order to learn how to create secure passwords, it’s useful to know how computers go about cracking them. If this doesn’t interest you, skip ahead to creating strong passwords.
How are passwords cracked?
Before we consider what makes a good password, let’s start by thinking about what makes a bad password. To understand what makes a bad password, we need to look at how passwords are cracked. The following is not aimed at people with computer science degrees and, as a result, some of the concepts have been simplified.
Brute force
This is probably the oldest form of password cracking and basically involves trying every possible combination of numbers, letters and characters. So, if an attacker knew that a password was 6 characters long, they might first try aaaaaa, then try aaaaab, then aaaaac and so on. Although this can take a long time — and it is not used much any more — it is guaranteed to correctly guess your password if given sufficient time.
In order to make it hard for brute force password crackers to get your password, you need to increase the number of options it has to try. The most common ways of doing this are:
- Increasing the number of characters available in each position of your password — use both cases, numbers and special characters.
- Increasing the length of your password
It’s worth noting that different programs will try passwords in different orders so starting your passwords with a z rather than an a provides little (if any) benefit.
Dictionary Attacks
It soon became apparent to password crackers that most people do not think like computers and use words rather than random characters as their passwords. To carry out a dictionary attack, the attacker provides a program with a list of passwords to try. The program will then try each of them. You can also provide these programs with rules such as “try putting a capital at the beginning” or “add a 1 at the end”. The actual rule sets that are added tend to be a lot longer than this and have been derived by looking at large sets of passwords that have been leaked. If you think that changing that i in your password to a 1 means your password is secure, think again.
If your password is derived from a common name, word or saying, you should assume that it will be cracked by a dictionary attack quite quickly.
In order to make it difficult for computers to crack passwords using dictionary attacks, you should try to not base your passwords on words. Unfortunately, as humans, we find it difficult to remember random characters and, if it isn’t complex enough, it will be easy for computers to crack using a brute force attack anyway. The best bet is to use several, unrelated words and add some symbols in between them.
How to create strong passwords
The first rule I would give anyone about creating passwords is don’t make them unless you absolutely have to. Humans are predictable and tend to follow patterns and our memory just isn’t that good.
In order to remember passwords, we make them personal. The problem with this is personal things are often easy to work out. Birthdays, anniversaries and pet names are examples of things that are easy to socially engineer out of people and are used in a huge percentage of passwords.
Wherever possible, don’t make passwords yourself. Get a computer to generate them for you. They can create (almost) random passwords for you that are long and they will then remember them for you. I will discuss how to use password managers in the next section. Using a password manager is the best option but there are situations where it is just not possible or practical.
In these situations, you will need to use a unique password that you can remember. This needs to be long in order to prevent a brute force attack and shouldn’t be a word to thwart dictionary attacks. The best policy I have seen is to start with four or five unrelated words. Try and make at least one of the words uncommon. You might pick:
- apple
- giraffe
- chicken pie
- abacus
- button
Put all of these together and you have a nice long password applegiraffechickenpieabacusbutton. This is 35 characters long but currently it is only lower-case. The next step is to capitalise some of the letters applegiraffEchickeNpiEabacusbutton. Here I have just capitalised the last letter of giraffe, chicken and pie.
The last thing to do is to add some symbols in. Again, where you do this is up to you, here I have added some after giraffe and after abacus: applegiraffE&chickeNpiEabacus£“£button
We now have a 41 character password with capitals, and symbols. Although this password doesn’t include numbers, it shouldn’t be difficult to see how to extend this to add numbers.
You may be thinking that you couldn’t possible remember this sort of password but I think you’d be surprised. For our brain, remembering 5 words isn’t that hard. For a computer, guessing 5 words is hard. Adding the symbols and the capitals makes it almost impossible for a computer to guess this password in any realistic amount of time. We’re talking about the age of billions of universes here.
It’s important to note that you don’t need to remember many of these. This sort of strong password is only for those situations where a password manager is not possible. You’ll probably only have to remember a few of these passwords.
Use a password manager
You should be using a password manager. Password managers are programs that store passwords. Most will also be able to generate passwords and for the purpose of this blog, I’ll assume that the password manager you choose does this.
Of course, your password manager will itself need a password. This needs to be the sort of password that we discussed in the previous section. If possible, enable 2 factor authentication as well which will mean accessing your passwords will require you to have a trusted device on hand.
By using a password manager, you’ll be able to use a different, secure password for every account you use. If the worst happens and one of your accounts is hacked, you don’t have to worry about your other accounts because they all have different passwords.
What if my password manager is hacked?
A common concern people have is that if a password manager is hacked then all of your accounts will be compromised. This will not be a problem though if you use a reputable password manager. All of the big players will store the passwords, encrypted with your secure password. This means that even if the password manager was hacked, the hacker wouldn’t be able to get your passwords without your master password.
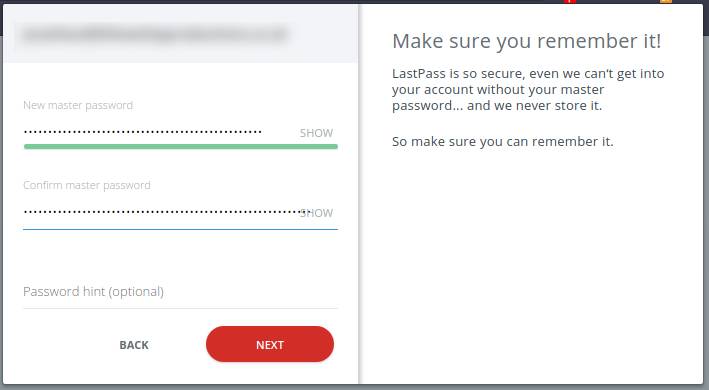
Source: Last Pass
What to check for when comparing password managers
Once you’ve realised that you should be using a password manager, you’ll need to choose one. There are plenty of good ones to choose from, but also plenty of bad ones. Here are some of the things to look out for. Not all of these will apply to everybody.
Browser extensions
You’ll probably want a password manager that integrates well with your browser of choice. This will allow it to automatically populate passwords for you when signing in.
Smartphone apps
Similarly to browser extensions, you will probably want a password manager that you can use on your phone.
Sync capabilities
If you use multiple devices, you might want to consider choosing a password manager that can sync your passwords between your devices. There is a caveat though. You need to make sure that the sync feature is a secure one (see below).
Local encryption / decryption
If you choose a password manager that can sync between devices, it is vital that you ensure the manager encrypts / decrypts your passwords on the machine you are using, not in the cloud.
Best password manager
There are many good ones but some of the most well known, and well trusted are:
Never reuse passwords
Finally, never re-use passwords. In case you’re wondering, adding a 1 to the end counts as re-use. If you’re using a password manager, creating new passwords for each account is easy, so you have no excuse.
If you’re still unsure about passwords, or security in general, please email us and we’ll try to help.